Price Manipulation on OpenDrive Files Storge App
[ads]
Price Manipulation on OpenDrive Files Storge App – Bug Bounty POC
This post is published by Bug Bounty POC on the request of Danyal Nasir as a guest writer.Note that the post is written by Danyal Nasir & any mistake in writing will be entertained only from him We allow anyone to write contents on our blog as a guest so other can also learn.If you’re interested in sharing your finding through Bug Bounty POC Platform contact us on facebook group or via email support@bugbountypoc.com.
Hello Bug Bounty POC viewers, myself Daniyal Nasir an independent security researcher. Today i’m going to share one of my finding regarding a security flaw which i found in OpenDrive web application platform few months ago.It was just a little find but the impact was too much High.
This is actually a Files Hosting Platform like Dropbox, Mediafire etc,having different kinds of free and premium packages plans.
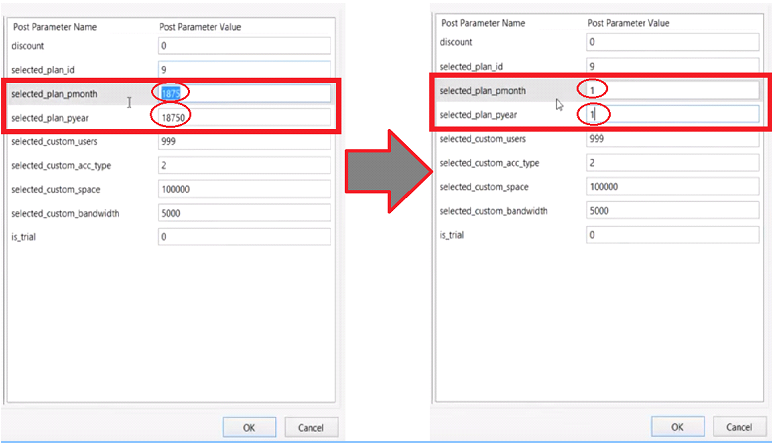
So, while testing the payment sections i’ve seen that they are validating the prices of the premium plan on the client-side as a parameter values and not confirming the price values by our plan configuration in the next step also.I wonder at that time, when i saw that there is a custom area where we can configure ourself the Account type, Account Space, Bandwidth and Users etc.So i set all the fields with the maximum values limit which worth $1875 (you can see in the below screenshot)

Price Manipulation on OpenDrive Files Storge App
So the attack vector was very simple and straight forward. By manipulating the values of the prices parameters, the price value got replaced with the new price ($1) which was set by me. (i used tamper data)
Price Manipulation on OpenDrive Files Storge App
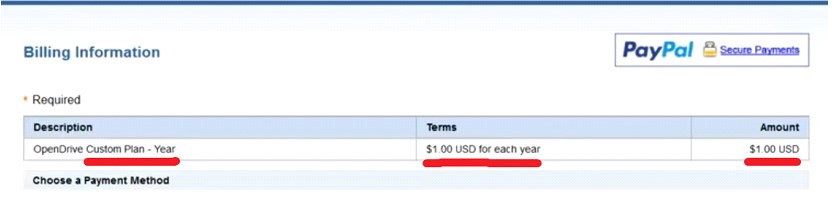
As i told you before, that they were also not detecting the price value by our plan configuration in the next step. So after changing the price value it redirected me to the final transaction vault where it confirmed my price with my plan configuration and gave me options to choose the payment method.
(Credit Card OR Paypal) i chose PayPal:

Price Manipulation on OpenDrive Files Storge App
After Selecting PayPal Payment Method, it redirects me to PayPal Gateway where i had to pay only 1$ instead of $1875 for my selected configured storage plan
As you guys saw that even a very little flaw can be result in a loss of thousands of dollars. I reported this security bug to the Opendrive Developers Team. They took this very seriously and released a quick fix of this vulnerability and i rewarded with a handsome bounty for this act.
Happy Sharing!











I have recently started a website, the information you offer on this web site has helped me greatly. Thanks for all of your time & work. “The only winner in the War of 1812 was Tchaikovsky” by Solomon Short.