Reflected XSS in Google Sandbox domain
[ads]
Reflected XSS in Google Sandbox domain – BugBountyPoc
Hello BugBountyPoc Viewers, my name is Florian Kunushevci, i’am an 16 years old ‘Security Researcher’ from Kosovo. Today i will share one of my old finding in google sandbox domain that how i found the Reflected xss in Google Sandbox Domain.Google Did not accept the bugs in Sandbox domain so I decide to share it with you all because it’s fun to know the method i used.
Reproduction Steps :
Creating the payload to execute:
1: Go to website jsbin.com
2: In the link put the Payload : “><script>alert(document.domain)</script>
3: Execute it as Javascript and copy the link.
4: You will get like output.jsbin.com/$linkpayload$
——————-
Injecting at googletranslate:
1: Go to the https://translate.google.com/
2: Put the link u gain at the translate section./ output.jsbin.com/$linkpayload$
3: It will appear like (Blue Link) click on it and you will see an XSS Alert./
Screenshot :
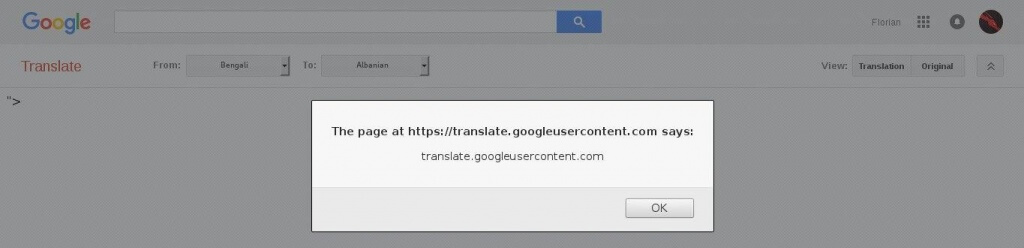
Reflected XSS in Google Sandbox domain
Hope you will learn something. Contact me on facebook if u have any questions: https://www.facebook.com/misteriozi.pirat.kwg












Thanks designed for sharing such a nice opinion, article is fastidious, thats why
i have read it entirely
use (document.location)
Some truly interesting points you have written.Aided me a lot, just what I was searching for : D.